Various Authentication Methods and Orchestration Templates
Make Security Policies More Intelligent.
Make Security Policies More Intelligent.
Multiple Authentication Methods
Flexible Configuration Templates
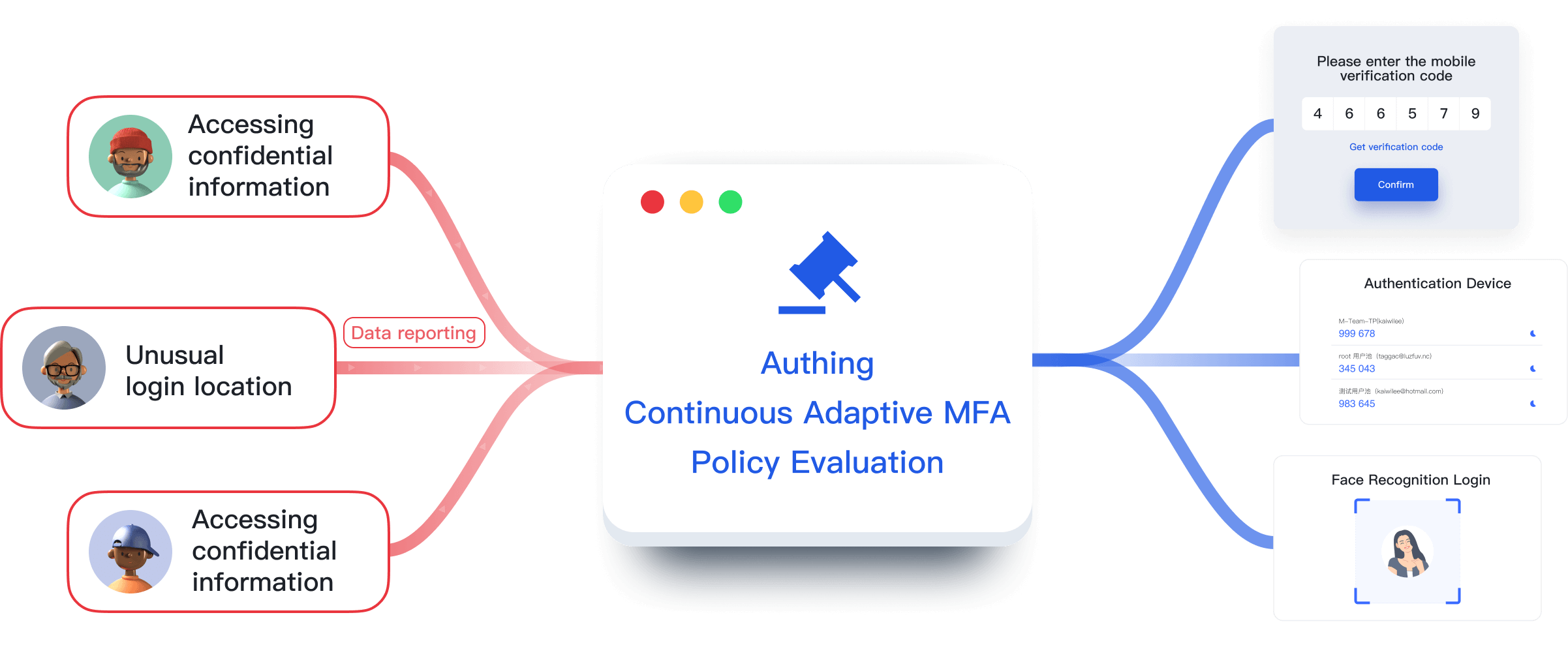
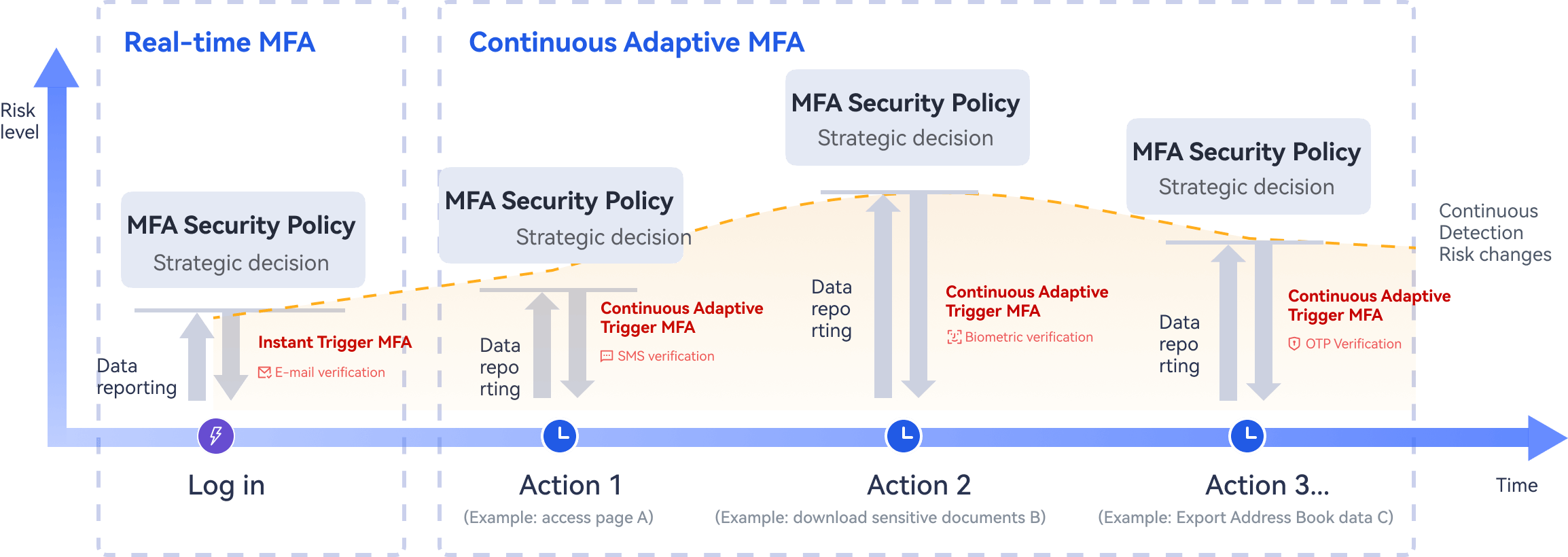
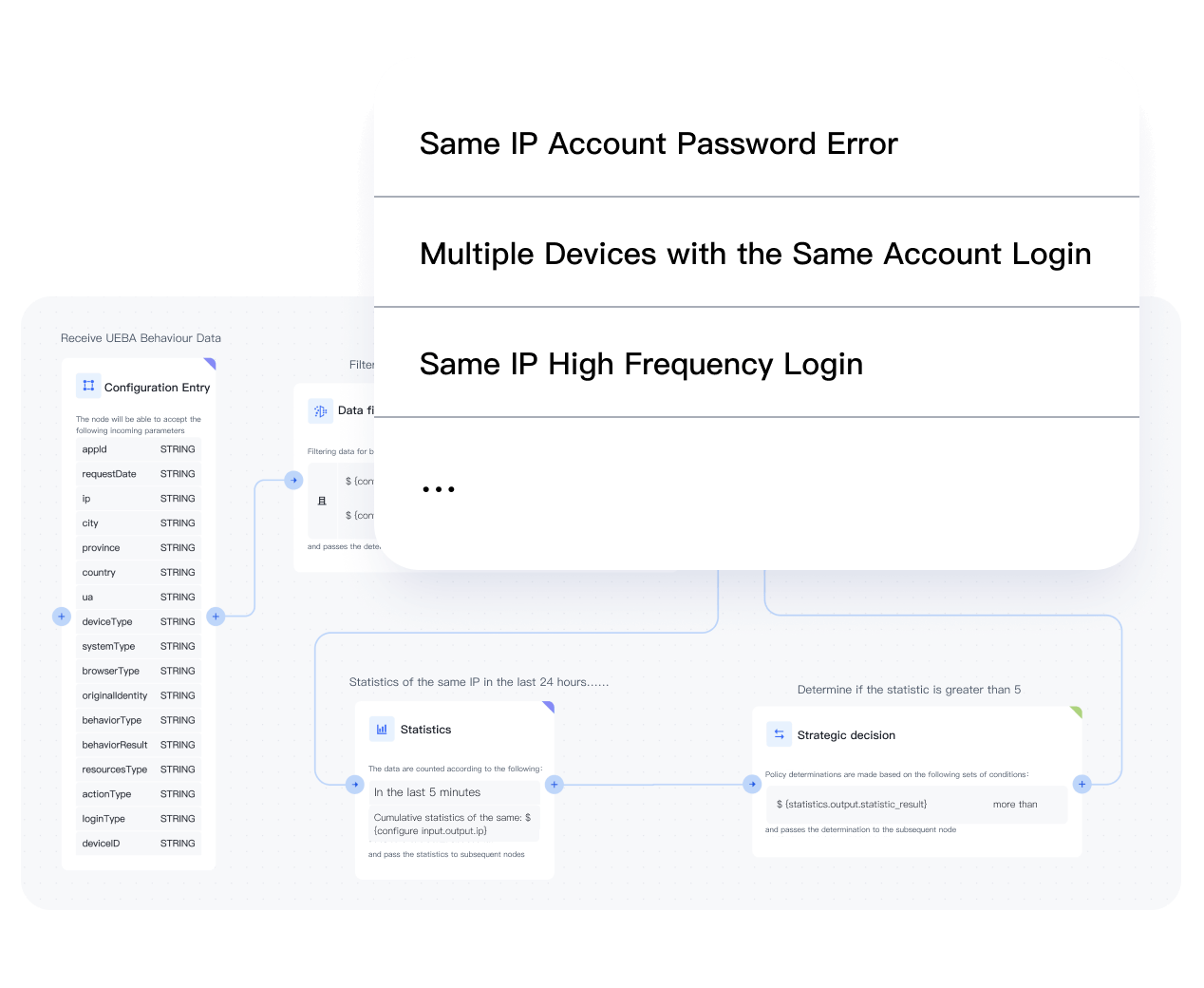
Dynamically detect user behaviour
While Ensuring Authentication Security,
We Also Consider Employee Efficiency and User Experience.
We Also Consider Employee Efficiency and User Experience.
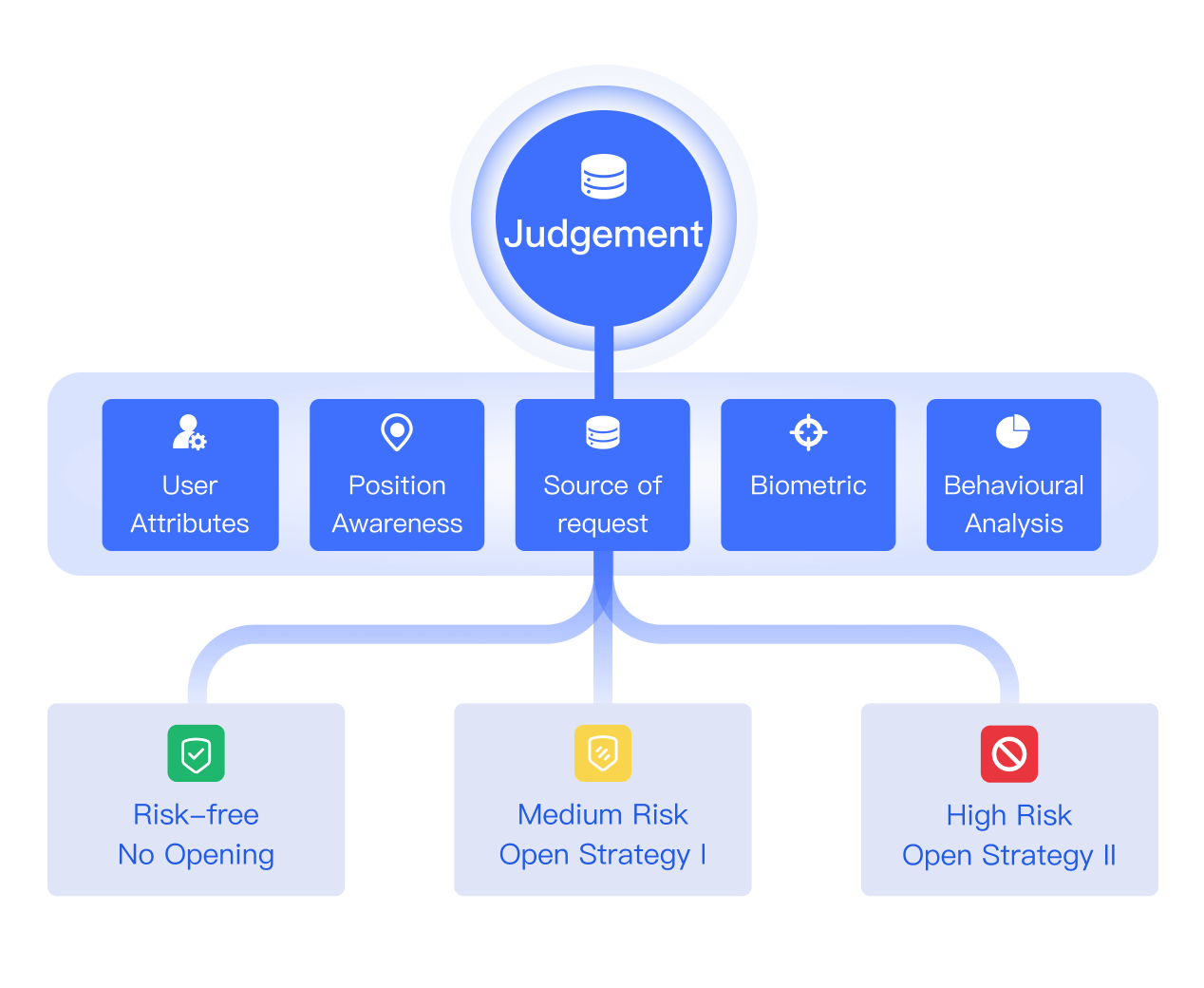
Adaptive security policy
Calling the API/SDK
Pre-integrated multiple terminals